- Browse
- Cloud Computing Security
Cloud Computing Security Courses
Cloud Computing Security courses can help you learn about risk assessment, data protection strategies, compliance frameworks, and incident response planning. You can build skills in threat modeling, vulnerability management, and implementing security controls across cloud environments. Many courses introduce tools like AWS Identity and Access Management, Azure Security Center, and various encryption technologies, showing how these skills are applied to safeguard data and maintain compliance in cloud infrastructures.
Popular Cloud Computing Security Courses and Certifications
 M
MMicrosoft
Skills you'll gain: Generative AI, Artificial Intelligence, Productivity, AI Enablement, LLM Application, Microsoft Copilot, Data Ethics, Responsible AI, Machine Learning, Natural Language Processing
Beginner · Course · 1 - 3 Months
 F
FFudan University
Skills you'll gain: Unity Engine, Mobile Development, Video Game Development, Cloud Deployment, Android (Operating System), Animation and Game Design, Data Analysis Software, User Accounts, User Interface (UI)
Intermediate · Course · 1 - 3 Months
 M
MMicrosoft
Skills you'll gain: Git (Version Control System), React.js, Version Control, Web Development Tools, GitHub, Debugging, Software Development Tools, Node.JS, Development Environment, Software Testing, Unit Testing, Maintainability, Server Side, UI Components, Javascript, Package and Software Management, Performance Tuning
Intermediate · Course · 1 - 4 Weeks
 P
PPontificia Universidad Católica del Perú
Skills you'll gain: Empathy, Safety and Security, Diversity Equity and Inclusion Initiatives, Legal Proceedings, Diversity Awareness, Student Support and Services, Higher Education, Medical Privacy, Conflict Management, Informed Consent, Investigation, Classroom Management
Mixed · Course · 1 - 3 Months
Skills you'll gain: R Programming, R (Software), Analysis, Mathematical Software, Data Analysis
Intermediate · Guided Project · Less Than 2 Hours

Skills you'll gain: Data Modeling, Enterprise Resource Planning, Dashboard, Business Intelligence, Data Visualization Software, Workflow Management, Pivot Tables And Charts, Data Import/Export, Extract, Transform, Load, Data Integration, Microsoft Excel, Data Transformation, Data Security, Scripting
Mixed · Course · 1 - 3 Months
 P
PPearson
Skills you'll gain: Front-End Web Development, Google Gemini, Web Development Tools, Generative AI, Database Management, Databases, Responsible AI, Back-End Web Development, Web Content, Web Development, User Interface (UI), ChatGPT, Web Servers, Prompt Engineering, Server Administration
Intermediate · Course · 1 - 4 Weeks

Skills you'll gain: Unreal Engine, Animation and Game Design, Video Game Development, 3D Assets, Game Design, Development Testing, Artificial Intelligence, User Interface (UI), Performance Tuning
Intermediate · Course · 1 - 3 Months

Skills you'll gain: Performance Tuning, Splunk, Role-Based Access Control (RBAC), Application Performance Management, System Monitoring, Distributed Computing, System Configuration, Data Management, Security Information and Event Management (SIEM), Enterprise Security, Data Security, Event Monitoring, Scalability, Data Pipelines, Real Time Data, Authentications
Mixed · Course · 1 - 3 Months

Skills you'll gain: Application Security, Incident Response, Intrusion Detection and Prevention, Network Security, Cybersecurity, Cyber Security Strategy, Cyber Attacks, Data Security, Hardening, Distributed Denial-Of-Service (DDoS) Attacks, Vulnerability Management, Vulnerability Assessments, Multi-Factor Authentication, System Configuration, Scripting, Linux Commands, Bash (Scripting Language), Linux, Scripting Languages, Python Programming
Mixed · Course · 1 - 4 Weeks
 A
AArizona State University
Skills you'll gain: Exploratory Data Analysis, Data Strategy, Unstructured Data, Data-Driven Decision-Making, Data Literacy, Solution Design, Data Analysis, Needs Assessment, Gap Analysis, Requirements Analysis
Beginner · Course · 1 - 4 Weeks

Skills you'll gain: MITRE ATT&CK Framework, Cyber Threat Hunting, Incident Response, Cyber Threat Intelligence, Threat Modeling, Digital Forensics, Threat Detection, Endpoint Detection and Response, Computer Security Incident Management, Microsoft Windows, Exploitation techniques, Threat Management, Exploit development, Cyber Security Strategy, Cyber Attacks, Cybersecurity, Cyber Security Policies, Anomaly Detection, Cyber Risk, Information Technology
Beginner · Course · 3 - 6 Months
Searches related to cloud computing security
In summary, here are 10 of our most popular cloud computing security courses
- Microsoft Ruta ExperiencIA: Microsoft
- 网络游戏设计与开发毕业项目: Fudan University
- JavaScript Development Tools and React: Microsoft
- Bienestar PUCP: prevención del hostigamiento sexual: Pontificia Universidad Católica del Perú
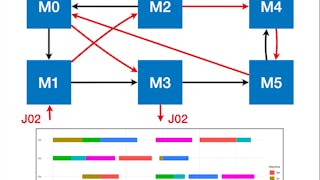
- Job Shop Scheduling Using MILP Optimization on RStudio: Coursera
- QlikView & QlikSense: Build & Analyze Data Models: EDUCBA
- Generative AI for Web Developers: Pearson
- Unreal Engine 5 – Create A Zombie Survivor FPS Game: Packt
- Splunk Administration & Performance Tuning: EDUCBA
- CyberSec First Responder – Advanced (CFR-A): Address: CertNexus










